Statutory definition, recent case law, contentious procedure, evidentiary methods and protection strategies — everything you need to know to safeguard your confidential information.
In an economy built on intangibles, a company’s value often lies in what it doesn’t disclose. Customer databases, algorithms, business strategies or technical know-how: these critical assets are not always patentable, and this is where trade secret protection comes into play.
Since the French law of July 30, 2018, transposing EU Directive 2016/943, France has had a powerful but demanding protective framework. The 2024-2025 case law has significantly clarified the relationship between trade secrets, the right to evidence and GDPR. This reference guide provides everything you need to understand, protect and defend your confidential information.
This guide covers:
- The legal definition and 3 cumulative protection criteria
- The 2024-2025 case law review and its practical implications
- Litigation procedures: taking legal action, timelines, costs
- Methods for proving the prior existence of your secret
- Industry case studies (pharma, tech, food & beverage)
- Coordination with other intellectual property rights
- The international dimension of protection
Evolution of the Legal Framework
| June 8, 2016 |
Adoption of EU Directive 2016/943 on trade secret protection |
| July 30, 2018 |
Transposition into French law (Law No. 2018-670) |
| December 22, 2023 |
French Plenary Court of Cassation: admissibility of unfairly obtained evidence under conditions (n°20-20.648) |
| June 5, 2024 |
French Commercial Chamber of the Court of Cassation: first articulation of the right to evidence with trade secrets (n°23-10.954) |
| February 5, 2025 |
French Commercial Chamber of the Court of Cassation: confirmation of the “indispensable” requirement (n°23-10.953) |
| February 27, 2025 |
CJEU: GDPR prevails over trade secrets for automated decisions (C-203/22) |
Fundamentals: What is a Trade Secret?
Unlike traditional intellectual property (patents, trademarks), which rests upon a public title, trade secret protection safeguards information by reason of its very secrecy. This protection arose from a simple observation: certain strategic information cannot, or should not, be patented.
The statutory definition (Article L.151-1 of the French Commercial Code)
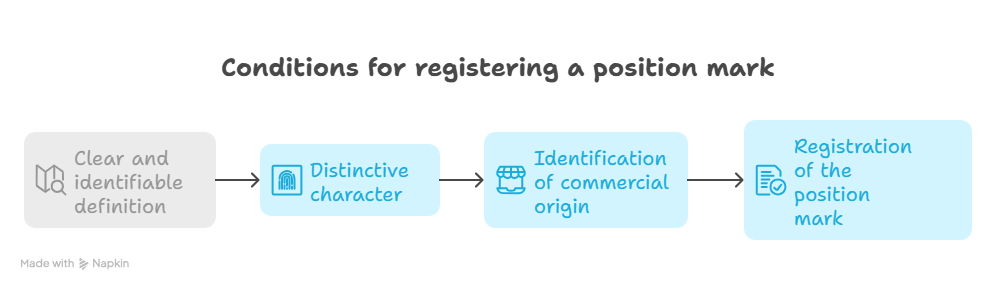
To benefit from statutory protection, information must satisfy three strict cumulative criteria set out in Article L.151-1 of the French Commercial Code:
1. The secret nature of the information
The information is not generally known or readily accessible to persons familiar with that type of information. This is the criterion of “non-obviousness”: the information must not be commonplace within the relevant sector.
2. Commercial value
The information has commercial value (actual or potential) precisely because it is secret. Such value may be direct (competitive advantage) or indirect (cost avoidance).
3. Reasonable protective measures
The information is the subject of concrete protective measures taken by its holder to preserve its secret nature. This is the criterion most often determinative in litigation.
Key point : If you do not actively protect your information (confidentiality clauses, passwords, document classification), the court will hold that no trade secret exists. This is the criterion most frequently overlooked by businesses.
What does a trade secret cover?
The scope is exceedingly broad. The notion of “information” is to be understood expansively and includes:
Technical know-how: manufacturing processes, recipes, chemical formulae, production methods, optimisation parameters, technical drawings.
Commercial information: client and prospect lists, pricing policies, supplier terms, product margins, internal market shares.
Strategic data: M&A projects, development plans, proprietary market studies, business plans, financial projections.
Organisational information: strategic organisational charts, management methods, optimised internal processes.
Algorithms and data: source code, scoring models, proprietary databases, software architectures.
What trade secrets do NOT protect
It is essential to grasp the limits of this protection:
Independent discovery: if a competitor develops the same information autonomously, you may not bring action against them.
Lawful reverse engineering: the analysis of a product placed on the market in order to ascertain its functioning is lawful (save for any contrary contractual stipulation).
Information that has become public: once a secret is disclosed (whether voluntarily or otherwise), protection lapses irrevocably.
General employee skills: the know-how acquired by an employee (his or her “experience”) belongs to that employee and may be employed in the service of a new employer.
Case law landscape 2024-2025
Recent judicial developments are marked by a sustained tension between two imperatives: the protection of corporate secrets and the right to evidence (the necessity for a party to obtain documents in order to vindicate its rights in court).
The seminal ruling: French Court of Cassation, Commercial Chamber, 5 February 2025 (n°23-10.953)
This decision marks the principal turning point. In a case opposing the franchise networks Speed Rabbit Pizza and Domino’s Pizza, the French Court of Cassation laid down a structural principle governing the equilibrium between these competing rights.
The judicial principle : “The right to evidence may justify the production of materials covered by trade secrets, provided that such production is indispensable to the exercise of that right and that the resulting interference is strictly proportionate to the aim pursued.”
Practical implications: for a court to order the production of a document covered by trade secrets, that document must be indispensable to the resolution of the dispute, and no longer merely “necessary” or “useful”. The term “indispensable” is deliberately restrictive: it excludes “fishing expeditions” (exploratory searches for evidence).
The court must conduct a proportionality assessment between the competing rights. This requires verifying that no alternative evidentiary means less injurious to the secret exist, and that the document sought is genuinely decisive for the outcome of the proceedings.
Management of seizures (saisie-contrefaçon and Article 145 of the French Code of Civil Procedure)
Where a company is subjected to an ex parte seizure on its premises, how can it prevent its trade secrets from reaching its competitors?
Case law imposes the strict application of provisional sequestration: documents seized which are liable to disclose trade secrets are placed under sequestration with a third party (typically the judicial commissioner). A one-month period is granted to the seized party to challenge the communicability of the documents. The court rules on transmission to the seizing party prior to any disclosure, by applying the proportionality test.
The preparatory ruling: Cass. Com., 5 June 2024 (n°23-10.954)
This decision laid the foundations of the doctrine, recognising for the first time that the right to evidence could justify an encroachment upon trade secrets, while requiring strict judicial supervision.
Unfairly obtained evidence: Plenary Assembly, 22 December 2023 (n°20-20.648)
The Plenary Assembly held that evidence obtained by unfair means (covert recordings, purloined documents) may be adduced in court provided that two conditions are satisfied: its production is indispensable to the exercise of the right to evidence, and the interference with the rights of the opposing party is proportionate to the aim pursued.
Trade Secrets vs GDPR: The CJEU Ruling of February 27, 2025
At the European level, the Court of Justice (CJEU, C-203/22, Dun & Bradstreet Austria) handed down a major decision concerning the articulation between trade secrets and the rights of natural persons.
The facts
An Austrian consumer was refused a mobile telephony contract on the grounds that her creditworthiness was deemed insufficient. This refusal rested upon an automated assessment (credit scoring) carried out by Dun & Bradstreet. She sought explanations as to the “underlying logic” of that decision, invoking Article 15 GDPR (right of access). The company refused on the ground of the trade secret protecting its algorithm.
The CJEU’s decision
Principle laid down by the CJEU : The GDPR prevails over trade secrets in matters of access rights to personal data and information concerning automated decisions. The data controller must provide “meaningful information about the underlying logic involved” in a manner that is “concise, transparent, intelligible and easily accessible”.
What this entails for businesses: the mere disclosure of an algorithm or a complex mathematical formula is not sufficient to discharge the duty of information. The explanation must be intelligible to a non-specialist.
The undertaking must enable the data subject to understand which data have been used and how they influenced the decision. This does not entail disclosure of the entire algorithm, but rather an explanation of the determinative criteria. In the event of litigation, allegedly protected information must be communicated to the court, which shall balance the competing rights.
Sectoral impact — This decision directly affects sectors employing automated scoring: banks and credit institutions, insurance (personalised pricing), recruitment (automated CV screening), residential leasing (tenant solvency), and more generally any automated decision-making process producing significant effects on individuals.
Protection Strategies: “Reasonable Measures”
To benefit from statutory protection, the undertaking must demonstrate that it has implemented concrete measures. The term “reasonable” denotes measures adapted to the nature of the information, the size of the undertaking, and the economic context. An SME does not have the same resources as a CAC 40 group, and the courts take this into account.
Protective measures checklist
Legal measures
• Non-disclosure agreements (NDAs): systematic prior to any discussion with a partner, service provider or investor
• Reinforced confidentiality clauses: in employment contracts and commercial contracts
• Non-competition clauses: for strategic positions, within statutory limits
• IT charter: expressly setting out the duties of confidentiality and signed by all collaborators
• Internal regulations: incorporating confidentiality obligations
Technical measures
• Access management: need-to-know principle
• Traceability: access logs for sensitive documents
• Encryption: of sensitive data both at rest and in transit
• Strong authentication: MFA for access to critical systems
• DLP (Data Loss Prevention): data leakage prevention tools
Organisational measures
• Document marking: “CONFIDENTIAL — TRADE SECRET” labelling on sensitive documents
• Information classification: tiered confidentiality system (C1, C2, C3, etc.)
• Team training: awareness of social engineering risks and information leakage
• Departure procedures: exit interview reminding obligations, retrieval of access credentials and documents
• Physical security: secure premises for sensitive paper documents
• Inventory of secrets: regular mapping of the undertaking’s confidential information
Practical advice : The “CONFIDENTIAL” marking of documents constitutes the simplest and most effective measure to evidence before a court. An unmarked document will rarely be regarded as falling within the scope of trade secret protection. Equally, invest in traceability: the ability to demonstrate who accessed which information and when proves invaluable in litigation.
Establishing your trade secret: timestamping methods
In the event of litigation, you will need to prove that you held the information prior to the alleged infringement. The creation date of a digital file does not constitute sufficient proof (such date may be altered). You must establish a certain date.
e-Soleau (INPI): the dematerialised version of the Soleau envelope
The most widely known and economical solution for SMEs, start-ups and individual inventors. Since 1 April 2024, the paper Soleau envelope has been definitively discontinued: only the e-Soleau service remains, fully dematerialised, in accordance with Decree n°2023-166 of 7 March 2023 and the amending order modifying the decree of 9 May 1986.
Principle: you submit online, via the procedures.inpi.fr portal, a digital file (PDF, image, ZIP archive), which is timestamped by the INPI. A digital fingerprint (SHA-256 hash) is computed and preserved within the INPI’s Electronic Archiving System, AFNOR-certified. A timestamped filing certificate is generated immediately upon payment.
Cost: €15 per 5-year period of conservation, for documents not exceeding 50 MB. Each additional 50 MB tranche costs €10, up to a global limit of 2 GB per filing.
Conservation period: since 8 April 2024, the maximum conservation period has been increased from 10 to 20 years. The initial filing is for 5 years, extendable in successive 5-year tranches up to a maximum of 20 years. Extensions may be requested at the time of filing or subsequently.
Technical capacity: up to 100 files may be included within a single e-Soleau, for a total maximum volume of 2 GB. The former seven-page-per-compartment limitation disappeared together with the paper version.
Advantages: simplicity, low cost, accessibility 24/7, established judicial recognition, AFNOR-certified archiving.
Limitations: does not constitute an industrial property title; confers solely an evidentiary effect of prior possession (and the benefit of personal prior possession in patent matters, Article L.613-7 of the French Intellectual Property Code); no direct international value.
Website: INPI – e-Soleau
Filing with a judicial commissioner or a notary
Traditional solution offering maximum evidentiary force under French law. Since 1 July 2022, bailiffs (huissiers de justice) and judicial auctioneers (commissaires-priseurs judiciaires) have been merged into a single profession: that of judicial commissioner (Order n°2016-728 of 2 June 2016). As from 1 July 2026, this title becomes exclusive.
Principle: a public officer ascertains the contents of a document on a given date and stores it. The report drawn up has evidentiary force unless and until rebutted.
Cost: variable depending on volume, generally between €100 and €500 for a simple filing.
Advantages: incontrovertible evidentiary force, universal acceptance by French courts, ability to deposit digital media.
Limitations: higher cost than e-Soleau, less agile procedure for frequent updates.
Blockchain timestamping
A modern solution, particularly suited to technology companies and frequent updates.
Principle: a digital fingerprint (SHA-256 hash) of your document is inscribed in a public blockchain (typically Bitcoin or Ethereum). Such inscription is immutable and timestamped. The European eIDAS Regulation (EU n°910/2014) recognises the legal value of qualified electronic timestamping.
Cost: a few euros per timestamp via specialised services, or integrable into your internal processes.
Advantages: automatable, suited to software development pipelines (CI/CD), low marginal cost, version-by-version traceability.
Limitations: judicial recognition still emerging in France (though steadily growing), requirement to retain the original document corresponding to the hash.
Service providers: Woleet, OriginStamp, KeeSign, or solutions integrated into document management platforms.
APP filing (software)
For source code and software, the Agence pour la Protection des Programmes (APP) provides a specialised filing service.
Principle: secure deposit of source code with a certain date, recognised as proof of prior possession.
Cost: from €120 (excl. VAT) for 5 years.
Comparative table of evidentiary methods
| Method |
Cost |
Evidentiary Weight |
Ideal for |
| e-Soleau (INPI) |
€15 / 5 years |
★★★★☆ |
SMEs, inventors, stable documents |
| Judicial commissioner / Notary |
€100-500 |
★★★★★ |
Strategic filings, foreseeable litigation |
| Blockchain |
€1-10 / hash |
★★★☆☆ |
Tech, source code, multiple versions |
| APP filing |
€120 / 5 years |
★★★★☆ |
Software, source code |
Bringing legal action: procedure, time limits and costs
Where an infringement of trade secrets is identified, several courses of action are available to the holder of the secret. The choice depends on urgency, the gravity of the infringement and the objectives pursued.
Competent jurisdiction
Judicial Court (formerly Tribunal de grande instance): competent for civil actions concerning trade secrets. This is the court of general jurisdiction.
Commercial Court (Tribunal de commerce): competent where the dispute opposes two traders or commercial companies and concerns acts of commerce.
Labour Court (Conseil du prud’hommes): competent where the infringement is committed by an employee within the framework of the employment relationship (although the action may be brought before the Judicial Court for non-employment-related aspects).
Available proceedings
Summary proceedings (urgency)
An expedited procedure enabling the obtaining of provisional measures. Conditions: urgency and absence of serious dispute, or existence of imminent harm. Hearing date: generally 2 to 4 weeks following the writ of summons. The court may order the provisional prohibition on using or disclosing the secret, the conservatory seizure of disputed products or documents, and a astreinte (financial penalty) to ensure compliance.
Substantive proceedings
A complete procedure leading to a definitive decision. Average duration: 12 to 24 months at first instance depending on complexity. Permits the obtaining of definitive damages, permanent injunctions and publication of the judgment.
Adapted seizure (Article L.152-3 of the French Commercial Code)
Ex parte procedure (without notice to the opposing party) enabling the recording of an infringement and the seizure of evidence. Application to the President of the Judicial Court. Execution by a judicial commissioner on the premises of the alleged infringer. Sequestration of sensitive items pending the decision on their communicability.
Limitation period
Limitation: 5 years — Civil actions in matters of trade secrets are barred after 5 years from the date on which the holder of the secret had knowledge, or ought to have had knowledge, of the last fact enabling the action (Article L.152-2 of the French Commercial Code). This period may be interrupted by formal notice or by service of a writ.
Estimated costs
| Procedure |
Attorney Fees (estimate) |
Ancillary Costs |
| Formal Notice |
€500 – €1,500 |
— |
| Simple summary proceedings |
€3,000 – €8,000 |
Judicial commissioner: €200-500 |
| Adapted seizure |
€5,000 – €15,000 |
Judicial commissioner: €1,000-3,000 |
| Substantive proceedings (1st instance) |
€10,000 – €50,000+ |
Court-appointed expert: variable |
These estimates are indicative and vary according to case complexity, firm reputation and geographic area.
Materials to be assembled prior to action
Before initiating proceedings, ensure you have the following elements:
Proof of prior possession: e-Soleau, filing with a judicial commissioner or notary, blockchain timestamping..
Proof of protection measures: signed NDAs, IT charters, access logs, document classification.
Proof of infringement: disclosed documents, infringing products, witness statements, correspondence.
Damage assessment: loss of revenue, lost R&D investments, reputational harm.
Sanctions and remedies
In the event of theft, misappropriation or unlawful disclosure, the law provides for extensive civil sanctions. The criminal dimension remains confined to ancillary offences such as theft, breach of trust or receiving stolen property.
What the court may order
Injunctive measures: prohibition on using, manufacturing, marketing or revealing the protected information. Such prohibition may be coupled with an astreinte (sum payable for each day of non-compliance).
Recall and destruction measures: recall of products from the market, destruction of documents, files or products incorporating the secret (“infringing goods”).
Publication of the decision: at the infringer’s expense, in newspapers or on websites, to remedy reputational harm.
Damages: calculated by reference to the negative economic consequences (lost profits, loss of opportunity), moral prejudice and the profits derived by the infringer through the infringement.
Statutory exceptions (Article L.151-8 of the French Commercial Code)
Trade secrets are not enforceable in certain situations involving overriding interests (Article L.151-8 of the French Commercial Code):
Exercise of the right to information: freedom of expression and freedom of the press, particularly to disclose information of public interest.
Whistleblowers: disclosure of unlawful activity or reprehensible conduct in order to safeguard the public interest (protection reinforced by the French Waserman Law of 2022).
Protection of a legitimate interest: notably the right to evidence, subject to the proportionality conditions established by 2025 case law.
Employee representatives: in the exercise of their functions (social and economic committee, trade union representatives).
Sector-specific case studies
Trade secret protection is implemented in different ways depending on the sector. The following examples illustrate the issues at stake and the recommended best practices.
Pharmaceutical industry and biotechnology
Typical case: Protection of development data
A laboratory develops a new molecule. Prior to filing a patent (which entails disclosure), all R&D data constitute critical trade secrets: pre-clinical trial results, formulations tested, observed side effects, synthesis processes.
Issue: a leak may enable a competitor to file a “pre-emptive” patent or develop a similar molecule.
Recommended specific measures:strict compartmentalisation of R&D teams (each team having access only to its segment of the project). Daily timestamped and signed laboratory notebooks. Reinforced NDAs with CROs (Contract Research Organizations). Clean room procedures for licensing negotiations.
Technology sector (start-ups, software publishers)
Typical case: Protection of algorithms and source code
A start-up develops a recommendation algorithm constituting its competitive advantage. The source code and model training parameters constitute trade secrets.
Issue: a developer departing for a competitor could recreate a similar solution.
Recommended specific measures: technical architecture restricting access to the complete code (microservices, modular access). Systematic blockchain timestamping of commits. Specific confidentiality clauses within developers’ employment contracts. Monitoring of code repositories (GitHub, GitLab) to detect leaks. Formalised exit interviews with reminder of obligations.
Agri-food
Typical case: Protection of recipes and processes
A food manufacturer holds a unique recipe (sauce, beverage, processed product) the secrecy of which is the cornerstone of its market positioning. The most celebrated example is that of Coca-Cola, whose formula has remained secret since 1886.
Issue: disclosure would enable immediate copying by competitors or private label brands.
Recommended specific measures: fragmentation of the recipe (different persons knowing different parts). Codification of ingredients (internal codes in lieu of actual names). Restricted physical access to sensitive production zones. Regular audits of key ingredient suppliers.
Consulting and professional services
Typical case: Protection of methodologies and client data
A consulting firm develops proprietary methodologies and holds strategic data on its clients. These elements constitute major intangible assets.
Issue: a consultant departing for a competitor takes with them their “contact book” and methods.
Recommended specific measures: formal documentation of methodologies bearing the “trade secret” mention. Strict policy on the use of client data (export prohibition, anonymisation). Non-solicitation clauses concerning clientele. Team training on the distinction between personal skills and corporate assets.
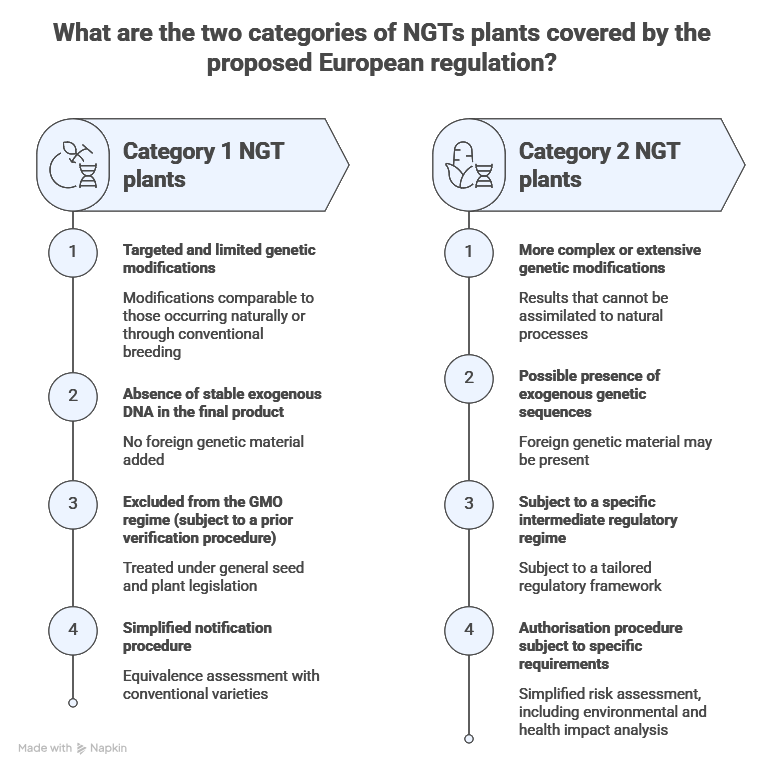
Interaction with other intellectual property rights
Trade secrets are not intellectual property rights in the strict sense, but they interact with other available protections. An effective protection strategy often combines several regimes.
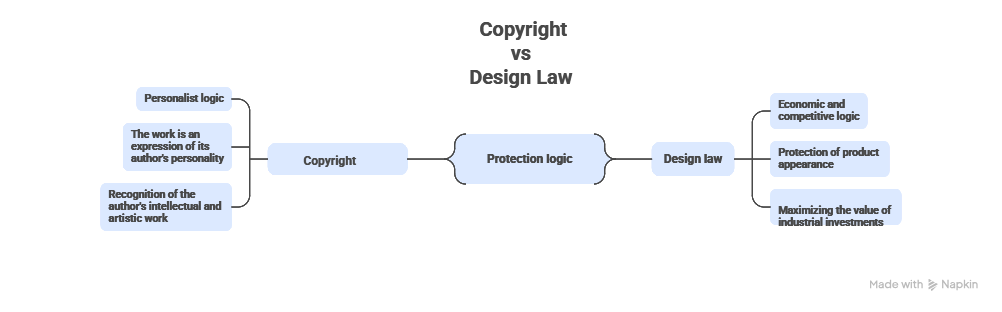
Trade Secrets and Copyright
Cumulative protection: the source code of a software programme may simultaneously benefit from copyright protection (which protects the original form of expression) and trade secret protection (which protects the underlying algorithms and business logic).
Key differences:
| Criterion |
Copyright |
Trade Secret |
| Formality |
None (automatic protection) |
Protection measures required |
| Subject of protection |
The original form |
The information itself |
| Duration |
70 years post mortem |
As long as secrecy is maintained |
Trade Secrets and Patents
Strategic choice: To patent or keep secret? This choice is fundamental and irreversible.
Patenting is preferable when: The invention is easily identifiable through reverse engineering. You want to monetize the invention (licenses, assignments). The commercial lifespan is less than 20 years. You need a title enforceable against all (including independent discoverers).
Trade secret is preferable where: the information does not satisfy the criteria for patentability. The secret can be sustainably maintained (no possible reverse engineering). The commercial life cycle exceeds 20 years. You wish to avoid the costs and the disclosure inherent in a patent.
Caution: a patent destroys the secret — Filing a patent entails publication of the invention (18 months after filing). Such disclosure is definitive: should the patent be invalidated or expire, the information remains in the public domain. The secret is forever lost.
Trade Secrets and Trademarks
Articulation: Trademarks protect a distinctive sign (public by nature), whereas trade secrets may protect the trademark strategy, positioning studies, and launch projects prior to public announcement.
Trade Secrets and Designs
Articulation: prior to the launch of a new design, the plans and prototypes constitute trade secrets. Once the product is marketed, protection passes to the design (registered or, within the EU, unregistered).
Trade secrets and know-how in contractual matters
In know-how license agreements or franchises, trade secrets are often the basis of the transferred value. Confidentiality clauses must be particularly carefully drafted, with a precise definition of the know-how scope, protection obligations for the licensee, and control mechanisms.
International Dimension
In a globalised economy, your trade secrets travel beyond borders. It is essential to grasp the international protection framework.
The Harmonized European Framework
EU Directive 2016/943 has harmonised protection across all 27 Member States. This means that the definition of trade secrets and the available remedies are similar throughout the European Union, thereby facilitating cross-border protection.
The TRIPS Agreement (WTO)
Article 39 of the Agreement on Trade-Related Aspects of Intellectual Property Rights (TRIPS) requires the 164 WTO members to protect “undisclosed information”. This is the minimum ground of international protection.
International Comparison
| Jurisdiction |
Protection Level |
Particularities |
| United States |
★★★★★ |
Defend Trade Secrets Act (DTSA, 2016). Federal action available. Punitive damages up to 2x. Ex parte seizures. |
| European Union |
★★★★☆ |
Harmonized Directive 2016/943. Civil protection. No harmonized criminal component. |
| United Kingdom |
★★★★☆ |
Common law + directive transposition (retained post-Brexit). Breach of confidence. |
| China |
★★★☆☆ |
Revised Anti-Unfair Competition Law (2019). Improved protection but variable enforcement. |
| Japan |
★★★★☆ |
Unfair Competition Prevention Act. Criminal provisions. Effective protection. |
Best Practices for International Protection
Adapt your NDAs to applicable law: An NDA governed by French law won’t have the same effectiveness before an American or Chinese court. Include choice of law and jurisdiction clauses.
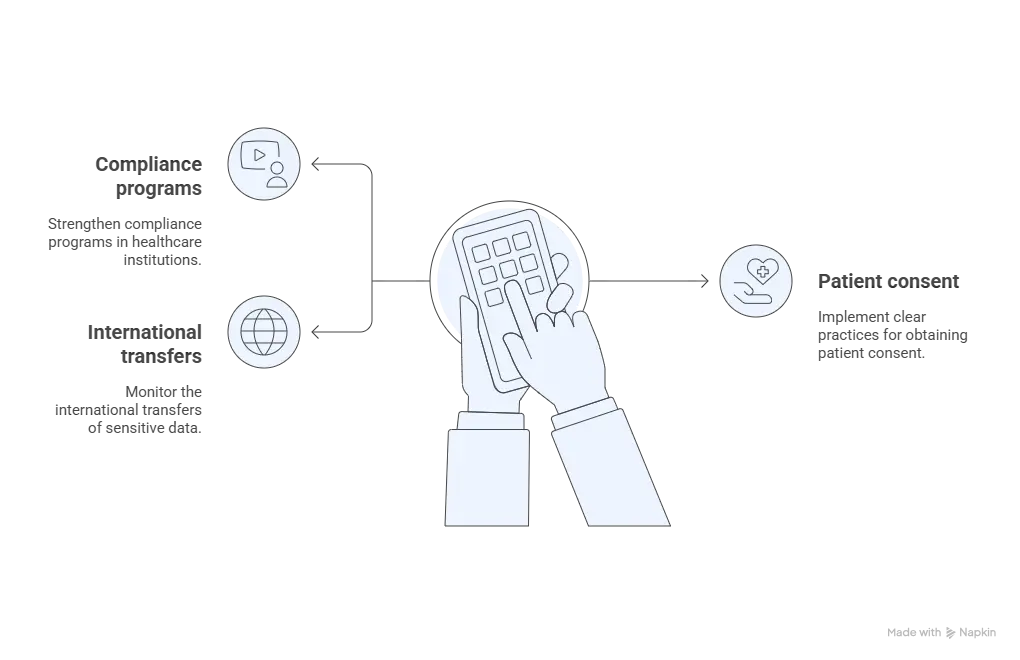
Map your information flows: Identify where your secrets transit (subsidiaries, subcontractors, cloud). Each jurisdiction crossed requires a protection analysis.
Reinforce clauses with foreign partners: In some countries with weaker protection, stricter contractual clauses (penalties, bank guarantees) can compensate.
Consider international arbitration: For cross-border disputes, arbitration (ICC, LCIA) can offer faster proceedings and facilitated enforcement in many countries (New York Convention).
Patent vs Trade Secret: Comparison Table
| Criterion |
Patent |
Trade Secret |
| Nature |
Public industrial property title |
Protection through confidentiality |
| Duration |
20 years maximum (with annuity payments) |
Unlimited as long as secrecy is maintained |
| Condition |
Public disclosure required |
Maintenance of secrecy required |
| Protection against |
All exploitation, including independent creation |
Unlawful acquisition only (not lawful reverse engineering) |
| Initial cost |
High (drafting, filing, examination: €5,000-15,000) |
Low (internal organizational measures) |
| Recurring cost |
Increasing annuities + international extensions |
Security measure maintenance |
| Main risk |
Design-around by different conception |
Leak or independent discovery |
| Monetization |
Easily monetizable (license, assignment, collateral) |
More complex monetization (due diligence required) |
| Ideal for |
Patentable technical inventions, monetization/licensing |
Know-how, commercial data, non-patentable information |
Combined Strategy
The two protections are not mutually exclusive. An optimal strategy can combine: patenting key innovations (strong, monetizable protection) and keeping complementary information secret (manufacturing processes, optimization parameters, implementation know-how).
12. Q&A: Your Questions About Trade Secrets
What is the difference between a patent and a trade secret?
A patent grants a 20-year monopoly in exchange for public disclosure of the invention. A trade secret protects information as long as it remains secret (unlimited duration), but does not protect against independent discovery by a competitor (lawful reverse engineering). A patent is enforceable against everyone; a trade secret only protects against unlawful acquisition.
Can an employee use their knowledge with a new employer?
Yes, acquired know-how (“experience”) belongs to the employee. The line is crossed if they take documents, client files or use specific technical secrets identified as confidential by their former employer. The distinction lies in the nature of the information: general skills (usable) vs. protected information (prohibited).
What constitutes a “reasonable protection measure”?
There is no official list, but case law recognizes: “Confidential” marking of documents, restricted computer access, signed confidentiality clauses, physical security of premises and staff training. Complete absence of such measures prevents legal protection. “Reasonable” is assessed according to company size and nature of the information.
Do trade secrets override whistleblower protections?
No. The law provides clear exceptions (Article L.151-8 of the Commercial Code). Trade secrets cannot be invoked to prevent disclosure of illegal activity or wrongdoing aimed at protecting the public interest (right to alert). The 2022 Waserman law strengthened this protection.
How long does protection last?
It is potentially perpetual. It lasts as long as the three conditions (secrecy, value, protection) are met. If the information becomes public — through disclosure, leak or independent discovery — protection is immediately and definitively lost. The example of Coca-Cola’s formula (kept secret since 1886) illustrates this potentially unlimited duration.
Can trade secrets yield to the right to evidence?
Yes, since the French Cour de cassation’s ruling of February 5, 2025 (No. 23-10.953). The judge must verify whether production of the document is “indispensable” to prove the alleged facts and whether the infringement of secrecy is “strictly proportionate” to the aim pursued. This is a case-by-case assessment that excludes exploratory requests.
Must I explain my algorithms to data subjects?
Since the CJEU ruling of February 27, 2025 (C-203/22), yes for automated decisions with significant effects (scoring, profiling). You must provide “meaningful information about the logic involved” in an understandable manner. This doesn’t mean disclosing the complete algorithm, but explaining the criteria used and their influence on the decision.
What is the limitation period for legal action?
Civil action is time-barred after 5 years from the day the trade secret holder knew or should have known the last fact enabling them to exercise their action (Article L.152-2 of the Commercial Code). This period can be interrupted by a formal notice or legal proceedings.
How can I prove I held the information before the infringement?
Several methods establish a certain date: e-Soleau (INPI, €15 for 5 years, up to 20 years’ conservation, filed online via procedures.inpi.fr since the discontinuation of the paper format in April 2024), filing with a judicial commissioner (formerly bailiff, since the merger of the professions on 1 July 2022) or notary, blockchain timestamping, or APP filing for software. The creation date of a digital file does not constitute sufficient proof, as it may be altered.
May source code be protected by both copyright and trade secrets?
Yes, these two protections can be combined. Copyright protects the original form of the code (automatically, without formalities), while trade secret law protects the underlying algorithms and business logic (provided the 3 legal criteria are met and confidentiality is maintained).
Legal References
Need to Audit Your Protection or Take Legal Action?
The Dreyfus law firm assists you in implementing your protective measures, drafting your NDAs, timestamping your trade secrets and defending your interests in the event of infringement.
Contact our experts
Dreyfus law works in partnership with a global network of lawyers specialised in intellectual property.
Nathalie Dreyfus with the support of the entire Dreyfus team.
This publication is intended to provide general guidance and to highlight certain issues. It is not designed to apply to specific situations and does not constitute legal advice.